Loading certificates with Azure Functions
Using certificates to secure, sign and validate information has become a common practice in the past couple of years. Therefore, it makes sense to use them in combination with Azure Functions as well.
As Azure Functions are hosted on top of an Azure App Service this is quite possible, but you do have to configure something before you can start using certificates.
Adding your certificate to the Function App
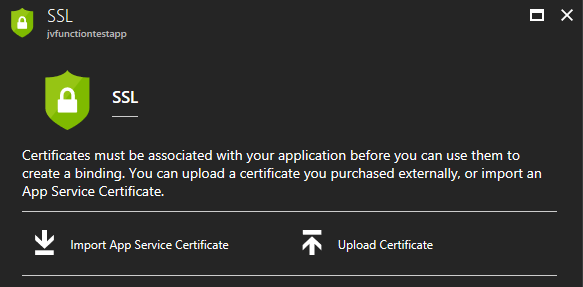
Let’s just start at the beginning, in case you are wondering on how to add these certificates to your Function App. Adding certificates is ‘hidden’ on the SSL blade in the Azure portal. Over here you can add SSL certificates, but also regular certificates
Keep in mind though, if you are going to use certificates in your own project, please just add them to Azure Key Vault in order to keep them secure. Using the Key Vault is the preferred way to work with certificates (and secrets).
For the purpose of this post I’ve just pressed the Upload Certificate-link, which will prompt you with a new blade from which you can upload a private or public certificate.
![clip_image001[4]](https://jan-v.nl/files/8047a43c-7dd3-4c73-8f80-f76e0789deb4.png)
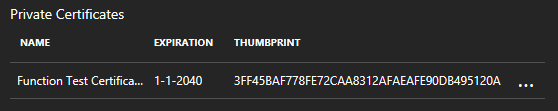
You will be able to see the certificate’s thumbprint, name and expiration date on the SSL blade if it has been added correctly.
There was a time where you couldn’t use certificates if your Azure Functions were located on a Consumption plan. Luckily this issue has been resolved, which means we can now use our uploaded certificates in both a Consumption and an App Service plan.
Configure the Function App
As I had written before, in order to use certificates in your code there is one little configuration matter which has to be addressed. By default the Function App (read: App Service) is locked down quite nicely which results in not being able to retrieve certificates from the certificate store.
The code I’m using to retrieve a certificate from the store is shown below.
private static X509Certificate2 GetCertificateByThumbprint()
{
var store = new X509Store(StoreName.My, StoreLocation.CurrentUser);
store.Open(OpenFlags.ReadOnly | OpenFlags.OpenExistingOnly);
var certificateCollection = store.Certificates.Find(X509FindType.FindByThumbprint, CertificateThumprint, false);
store.Close();
foreach (var certificate in certificateCollection)
{
if (certificate.Thumbprint == CertificateThumprint)
{
return certificate;
}
}
throw new CryptographicException("No certificate found with thumbprint: " + CertificateThumprint);
}
Note, if you upload a certificate to your App Service, Azure will place this certificate inside the CurrentUser/My store.
Running this code right now will result in an empty certificateCollection collection, therefore a CryptographicException is thrown. In order to get access to the certificate store we need to add an Application Setting called WEBSITE_LOAD_CERTIFICATES. The value of this setting can be any certificate thumbprint you want (comma separated) or just add an asterisk (*) to allow any certificate to be loaded.
After having added this single application setting the above code will run just fine and return the certificate matching the thumbprint.
Using the certificate
Using certificates to sign or validate values isn’t rocket science, but strange things can occur! This was also the case when I wanted to use my own self-signed certificate in a function.
I was loading my private key from the store and used it to sign some message, like in the code below.
private static string SignData(X509Certificate2 certificate, string message)
{
using (var csp = (RSACryptoServiceProvider)certificate.PrivateKey)
{
var hashAlgorithm = CryptoConfig.MapNameToOID("SHA256");
var signature = csp.SignData(Encoding.UTF8.GetBytes(message), hashAlgorithm);
return Convert.ToBase64String(signature);
}
}
This code works perfectly, until I started running it inside an Azure Function (or any other App Service for that matter). When running this piece of code I was confronted with the following exception
`System.Security.Cryptography.CryptographicException: Invalid algorithm specified.
at System.Security.Cryptography.CryptographicException.ThrowCryptographicException(Int32 hr)
at System.Security.Cryptography.Utils.SignValue(SafeKeyHandle hKey, Int32 keyNumber, Int32 calgKey, Int32 calgHash, Byte[] hash, Int32 cbHash, ObjectHandleOnStack retSignature)
at System.Security.Cryptography.Utils.SignValue(SafeKeyHandle hKey, Int32 keyNumber, Int32 calgKey, Int32 calgHash, Byte[] hash)
at System.Security.Cryptography.RSACryptoServiceProvider.SignHash(Byte[] rgbHash, Int32 calgHash)
at System.Security.Cryptography.RSACryptoServiceProvider.SignData(Byte[] buffer, Object halg)`
So, an Invalid algorithm specified? Sounds strange, as this code runs perfectly fine on my local system and any other system I ran it on.
After having done some research on the matter, it appears the underlying Crypto API is choosing the wrong Cryptographic Service Provider. From what I’ve read the framework is picking CSP number 1, instead of CSP 24, which is necessary for SHA-256. Apparently there have been some changes on this matter in the Windows XP SP3 era, so I don’t know why this still is a problem with our (new) certificates. Then again, I’m no expert on the matter.
If you are experiencing the above problem, the best solution is to request new certificates created with the Microsoft Enhanced RSA and AES Cryptographic Provider (CSP 24). If you aren’t in the position to request or use these new certificates, there is a way to overcome the issue.
You can still load and use the current certificate, but you need to export all of the properties and create a new RSACryptoServiceProvider with the contents of this certificate. This way you can specify which CSP you want to use along with your current certificate.
The necessary code is shown in the block below.
private static string SignData(X509Certificate2 certificate, string message)
{
using (var csp = (RSACryptoServiceProvider)certificate.PrivateKey)
{
var hashAlgorithm = CryptoConfig.MapNameToOID("SHA256");
var privateKeyBlob = csp.ExportCspBlob(true);
var cp = new CspParameters(24);
var newCsp = new RSACryptoServiceProvider(cp);
newCsp.ImportCspBlob(privateKeyBlob);
var signature = newCsp.SignData(Encoding.UTF8.GetBytes(message), hashAlgorithm);
return Convert.ToBase64String(signature);
}
}
Do keep in mind, this is something you want to use with caution. Being able to export all properties of a certificate, including the private key, isn’t something you want to expose to your code very often. So if you are in need of such a solution, please consult with your security officer(s) before implementing!
As I mentioned, the code block above works fine inside an App Service and also when running inside an Azure Function on the App Service plan. If you are running your Azure Functions in the Consumption plan, you are out of luck!
Running this code will result in the following exception message.
Microsoft.Azure.WebJobs.Host.FunctionInvocationException: Exception while executing function: Sign ---> System.Security.Cryptography.CryptographicException: Key not valid for use in specified state. at System.Security.Cryptography.CryptographicException.ThrowCryptographicException(Int32 hr) at System.Security.Cryptography.Utils.ExportCspBlob(SafeKeyHandle hKey, Int32 blobType, ObjectHandleOnStack retBlob) at System.Security.Cryptography.Utils.ExportCspBlobHelper(Boolean includePrivateParameters, CspParameters parameters, SafeKeyHandle safeKeyHandle) at Certificates.Sign.SignData(X509Certificate2 certificate, String xmlString) at Certificates.Sign.Run(HttpRequestMessage req, String message, TraceWriter log) at lambda_method(Closure , Sign , Object[] ) at Microsoft.Azure.WebJobs.Host.Executors.MethodInvokerWithReturnValue2.InvokeAsync(TReflected instance, Object[] arguments) at Microsoft.Azure.WebJobs.Host.Executors.FunctionInvoker2.<invokeasync>d__9.MoveNext()
My guess is this has something to do with the nature of the Consumption plan and it being a ‘real’ serverless implementation. I haven’t looked into the specifics yet, but not having access to server resources makes sense.
It has taken me quite some time to figure this out, so I hope it helps you a bit!
